Category:
Geopolitical AnalysisDistributed Risk: Open-Source as Geopolitical Power

Open-source software (OSS) has become the backbone of modern digital infrastructure, playing a critical role in government services, financial systems, and defense technologies. This widespread integration of OSS has created a new frontier for geopolitical influence and risk management.
The Rise of Open-Source Software 🌐
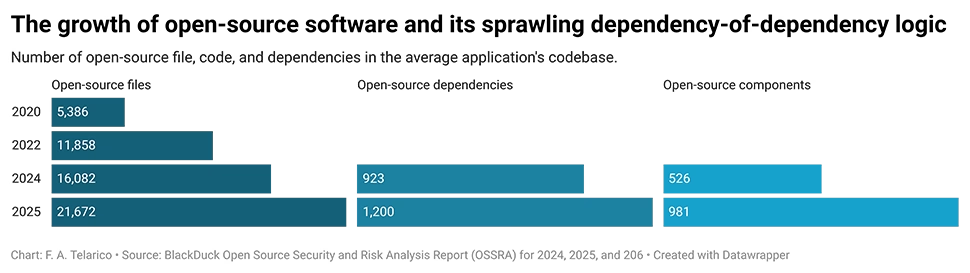
Open-source software is not just a technical marvel but a strategic asset. Recent audits reveal that 96% of commercial applications contain open-source components, underscoring the global dependency on OSS. This reliance introduces potential vulnerabilities, as actors capable of compromising these software components can exert significant influence across various sectors.
Geopolitical Implications of Software Supply Chains
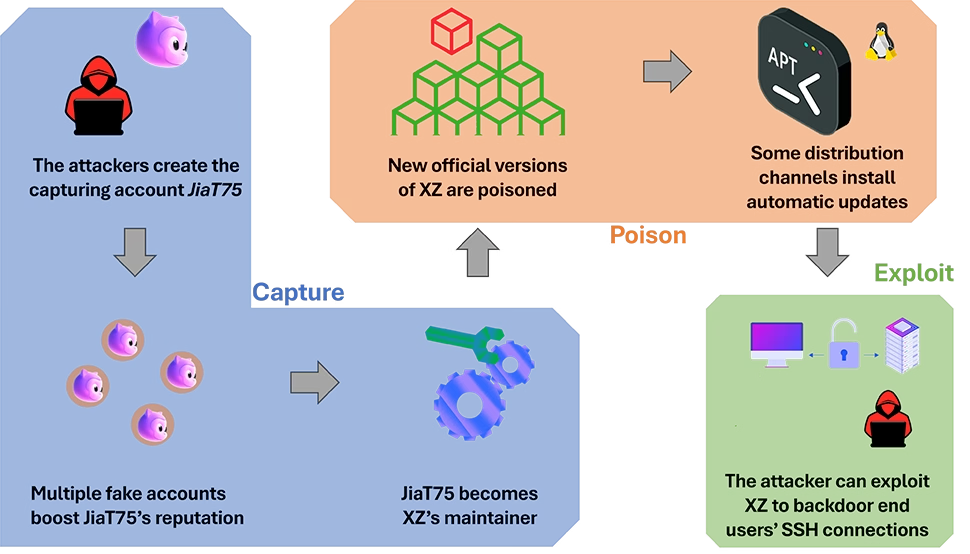
The 2020 SolarWinds attack and the 2021 Log4Shell incident highlighted the vulnerabilities inherent in software supply chains. However, it was the 2024 XZ incident that underscored the potential scale of these threats. This sophisticated attack involved the insertion of malicious code into XZ Utils, a widely-used software package, aiming to compromise the SSH protocol.
Such incidents highlight the growing importance of software provenance and security. The EU's Cyber Resilience Act is a response, imposing cybersecurity requirements on digital products. Other countries, including South Korea and the UK, have also introduced measures to strengthen software supply-chain security.

Understanding Upstream Supply-Chain Attacks
Upstream supply-chain attacks, like those involving the XZ Utils and Axios package, manipulate software delivery mechanisms. These attacks can propagate malicious code at scale, highlighting the need for enhanced security measures. In 2026, Google and Microsoft attributed a supply-chain compromise of the Axios OSS package to North Korea-linked actors, demonstrating the potential for geopolitical exploitation.
Strategic Control through Compliance and Security
Actors setting compliance baselines and security standards increasingly influence market conditions and interoperability. China's amended Cybersecurity Law and the UK's Cyber Security and Resilience Bill exemplify this trend. Control over software security is becoming a key element of geopolitical power.
The CPE Framework: Capture, Poison, and Exploit
Understanding OSS-related risks requires distinguishing between capture, poison, and exploit vectors:
- Capture involves manipulating project governance to introduce malicious changes.
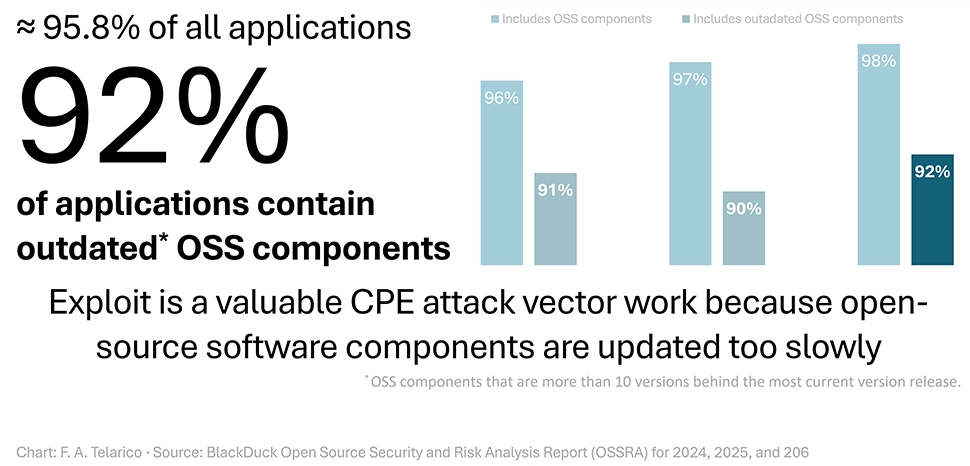
- Poison targets systems via indirect attacks through software distribution layers.
- Exploit refers to leveraging compromised software for broader malicious activities.
The strategic importance of OSS security is evident as these attack vectors become more prevalent.
Conclusion: The Future of Open-Source as Strategic Infrastructure
As open-source software continues to underpin critical infrastructure globally, its strategic significance will only grow. Nations and corporations must prioritize security and compliance to mitigate risks and leverage OSS as a tool of geopolitical power. The ongoing evolution of software supply-chain threats requires vigilant and proactive measures to safeguard digital sovereignty and security.
Looking ahead, the development of robust international standards and collaborative cybersecurity frameworks will be essential in addressing the complex challenges posed by OSS dependency. By understanding and adapting to these dynamics, stakeholders can navigate the intricate landscape of distributed risk and harness OSS for strategic advantages.
You May Also Like

Geopolitical Analysis
The Radev Risk: Bulgaria’s Strategic Balancing Act
May 13, 2026

Geopolitical Analysis
Vietnam's Starlink Pilot: A Digital Sovereignty Milestone
May 13, 2026

Geopolitical Analysis
Credibility Index: Assessing US Power Resilience
May 12, 2026

Geopolitical Analysis
US Pressure on Cuba: A New Geopolitical Era
May 12, 2026